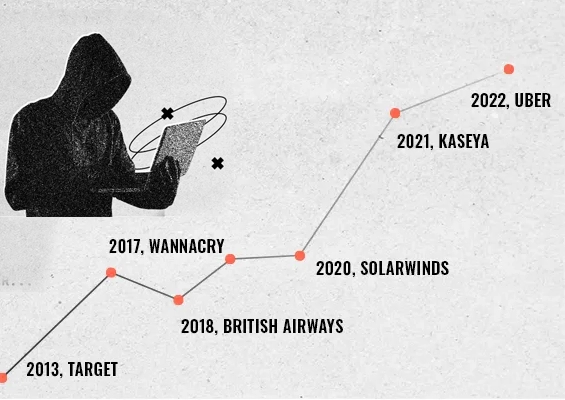
As cyberattacks evolve, password breaches continue to be one of the most exploited entry points for attackers. February 2025 was no exception, with several enterprises across finance, defence, telecom, and food delivery reportedly falling victim to compromised credentials, credential leaks, and weak authentication practices. These incidents highlight the growing vulnerabilities associated with password mismanagement, emphasizing the urgent need for better access controls, stronger authentication measures, and continuous monitoring of exposed credentials.
In this month’s roundup, we examine five major security breaches that allegedly stemmed from password-related vulnerabilities and discuss what businesses can learn from these incidents to strengthen their defences.
Zacks Investment Research Breach – A Devastating Credential Compromise
The Zacks Investment Research breach was a stark reminder of how a single set of compromised credentials can unravel an entire organization’s security infrastructure. Though this organization experienced this attack in June 2024, they have recently disclosed their data loss in February 2025. Attackers reportedly gained domain administrator access, which allowed them to infiltrate critical internal systems, steal usernames, passwords, email addresses, phone numbers, and even access Zacks’ source code repositories. The breach affected nearly 12 million user accounts, making it one of the most significant credential-related breaches of the year.
What makes this breach particularly concerning is the level of access the attackers allegedly achieved. Once they obtained admin credentials, they could move laterally within the organization, exfiltrating sensitive data without triggering security alerts. This incident highlights the dangers of relying solely on static passwords, as even complex credentials can be compromised. Organizations must adopt automated password rotation, multi-factor authentication (MFA), and real-time monitoring to mitigate the risk of unauthorized access. Additionally, businesses should implement least privilege principles, ensuring that employees and third parties only have access to the credentials they absolutely need. By enhancing password security and continuous authentication mechanisms, companies can significantly reduce the impact of credential-based attacks.
(Source: Fox59)Finastra Breach – The Threat to Global Financial Institutions
The financial sector remains a top target for cybercriminals, and the Finastra breach in February reinforced this reality. Finastra, which provides technology solutions to 8,100 financial institutions, including 45 of the top 50 global banks, suffered a breach where attackers allegedly gained access to sensitive financial data. While Finastra has not officially disclosed the attack vector, security researchers suspect a compromised employee credential was the primary entry point.
The financial industry faces unique risks due to its reliance on legacy authentication systems and complex third-party integrations, both of which expand the attack surface for credential theft. The attack on Finastra highlights a critical issue: weak or stolen passwords in financial institutions can lead to large-scale disruptions. The best defence against such breaches includes Zero Trust security frameworks, automated password rotation, and enforcing Multi-Factor Authentication (MFA) across all access points. Companies must also implement continuous monitoring for unauthorized credential usage to detect breaches before they escalate.
(Source: Bleeping Computer)Take control of your organization's password security today!
Defence Contractors’ Credentials Leak – A National Security Risk
One of the most alarming breaches of February 2025 was the leak of hundreds of compromised credentials from major U.S. defence contractors, including Lockheed Martin, Boeing, and Honeywell. This breach, unlike a traditional cyberattack, was allegedly a result of infostealer malware that harvested login credentials from infected employee devices. These credentials were later found on dark web forums, exposing national security-sensitive accounts to espionage, sabotage, and insider threats.
Perhaps even more concerning was the theft of session tokens, which allowed attackers to bypass MFA altogether. This attack demonstrates the limitations of traditional authentication systems, particularly when attackers find ways to hijack active login sessions. Companies dealing with sensitive government contracts must prioritize endpoint security, adopt biometric authentication, and deploy password-less authentication solutions to prevent such large-scale credential leaks. Furthermore, dark web monitoring and real-time alerting for exposed credentials should be standard practice in all high-risk industries.
(Source: Security Magazine)Orange Telecom Breach – The Risks of Employee Account Compromise
Telecom companies remain a prime target for cybercriminals, and February saw Orange Telecom’s Romanian division fall victim to a breach that allegedly exposed 380,000 email addresses and leaked 12,000 internal documents. While the exact method of attack remains unclear, security researchers believe that compromised employee credentials played a critical role in allowing unauthorized access.
This breach highlights an often-overlooked attack vector—employee account compromise. Even if no direct password database leaks occurred, exposed email credentials can be weaponized in phishing campaigns, credential stuffing attacks, or further social engineering exploits. Many organizations still fail to implement stringent password hygiene policies, leaving accounts vulnerable to basic brute-force and dictionary attacks.
(Source: Bleeping Computer)Lessons Learned: Strengthening Password Security in 2025
The security incidents of February 2025 reinforce an undeniable truth—password security remains one of the weakest links in enterprise cybersecurity. Whether it’s privileged credential abuse, credential leaks, or stolen session tokens, businesses must move beyond static passwords and adopt modern authentication strategies.
To minimize risks, organizations must:
- Eliminate password reuse by enforcing randomized, complex credentials.
- Implement Multi-Factor Authentication (MFA) to add an extra layer of security against credential-based attacks.
- Adopt password-less authentication using biometrics, hardware security keys, or authentication apps to reduce reliance on traditional passwords.
- Continuously monitor for leaked credentials through Dark Web Monitoring tools to detect and mitigate credential leaks before they are exploited.
- Enforce automated password rotation policies to prevent attackers from leveraging stolen credentials for extended periods.
With cyber threats evolving rapidly, organizations must shift from a reactive to a proactive security approach. Instead of waiting for a breach to occur, companies must prioritize identity security and access control as a fundamental part of their cybersecurity strategy.
How Securden’s Password Manager Can Help Prevent Credential-Related Breaches
Given the increasing sophistication of credential-based attacks, organizations must invest in advanced password security solutions that help eliminate risks associated with password misuse, leaks, and unauthorized access. Securden’s Enterprise Password Manager- Password Vault offers a comprehensive approach to securing credentials and privileged access.
Key features of Securden’s Password Manager include:
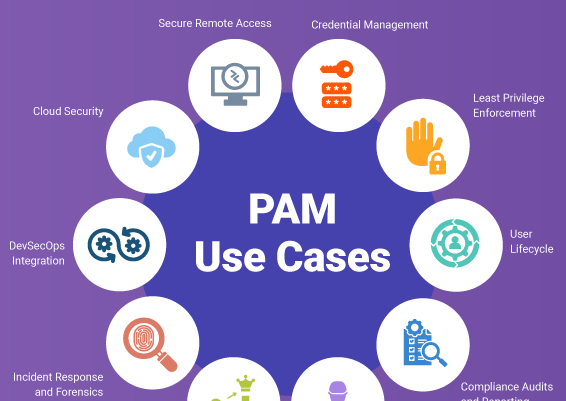
- Centralized Password Vaulting – Secure all enterprise passwords in a highly encrypted vault with role-based access control to ensure only authorized personnel can access credentials.
- Automated Password Rotation – Enforce automatic password changes at regular intervals to reduce the risk of long-term credential exposure.
- Multi-Factor Authentication (MFA) Enforcement – Add an additional layer of security to prevent attackers from using stolen credentials.
- Dark Web Monitoring – Continuously scan for leaked enterprise credentials, providing instant alerts when an organization’s passwords appear on dark web forums.
- Session-Based Access Control – Grant temporary, audited access to privileged accounts for contractors or employees, preventing persistent access risks.
By implementing Securden’s Password Manager, enterprises can reduce the likelihood of credential-related breaches, enhance security postures, and maintain compliance with global cybersecurity standards.
Say goodbye to password risks and hello to security!
Protect your credentials with Securden's Password Vault







![What is Cloud PAM? [Definition, Features, Benefits, and Factors to Choose the Right One]](/images/cloud-pam/cloud-pam-blog-image.webp)